Vulnerability Assessment
Cybersecurity-VAPT
Cybersecurity-VAPT identifies and addresses security weaknesses in systems, networks, and applications through rigorous testing, helping organizations prevent breaches and strengthen overall security.
All Services
Chosen by Leading Companies Across the Entire Globe
Companies of all sizes rely on our chatbot for better customer experiences.
Vulnerability Assessment & Penetration Testing (VAPT)
Proactive VAPT Services to Identify and Eliminate Security Vulnerabilities
Detect security weaknesses across applications, networks, and cloud environments through comprehensive vulnerability assessments and real-world penetration testing.
The Security Risk Challenge
Organizations today operate complex digital environments that are constantly targeted by cyber threats.
Overview
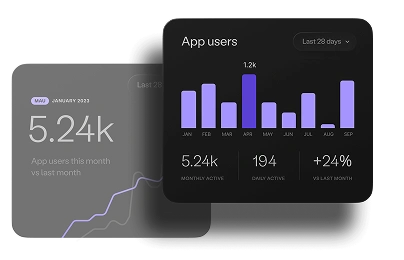
VAPT combines automated vulnerability scanning with manual penetration testing to uncover security gaps and validate how attackers could exploit them. This approach helps organizations strengthen defenses, prioritize risks, and maintain compliance across digital systems.
Our VAPT Implementation Approach
What We Enable
Detects security weaknesses across applications, networks, and cloud infrastructure before they can be exploited.
Simulate real-world cyberattacks through penetration testing to validate exploitability and identify security misconfigurations.
Prioritize vulnerabilities based on business impact and provide clear remediation guidance for IT and development teams.
Make legacy documents searchable and usable across enterprise systems.
Business Impact
Identify and eliminate vulnerabilities before attackers exploit them.
Detect high-risk vulnerabilities early and prioritize remediation.
Support regulatory frameworks such as ISO 27001, SOC 2, PCI-DSS, and GDPR.
Provide development and IT teams with actionable security insights.
Why Choose Us for VAPT?
Secure Your Systems Before Attackers Do
Ready to identify vulnerabilities before attackers do?
